AI-Driven Crypto Security
Crypto has matured but so have the criminals. From “pig-butchering” investment scams to cross-chain laundering and exchange-draining exploits, fraud is now faster and more adaptive. AI-driven crypto security changes the balance by spotting weak signals at machine speed, correlating on-chain activity with off-chain intelligence, and auto-responding before losses compound.
The scale is urgent: the U.S. FTC reported $5.7B in investment-scam losses in 2024, with crypto a major payment rail, while FBI IC3 recorded $6.5B+ in investment-fraud losses, largely crypto-linked. Federal Trade Commission+2Consumer Advice+2 Chainalysis shows 2025 thefts have already surpassed full-year 2024 by mid-year, underscoring the need for proactive controls.
This guide shows how AI-driven crypto security works in production covering data, models, real-time response, team workflows, and governance plus concrete steps to reduce scam exposure across exchanges, DeFi apps, wallets, and compliance teams.
The Fraud Landscape Crypto Teams Face in 2025
Investment scams & pig-butchering
Consistent top loss driver for consumers.Elder-targeted fraud
Over-60s suffer outsized losses in crypto fraud.Large-scale hacks
2025 YTD theft > $2.17B by July (incl. Bybit incident), outpacing 2024.Global criminal networks
Coordinated “scam factory” operations laundering funds via stablecoins.
Why this matters
Fraud patterns evolve fast across chains and social platforms. Static rules fall behind. AI-driven crypto security brings behavior modeling and anomaly detection to the front line.
What “AI-Driven Crypto Security” Actually Means
AI-driven crypto security fuses three layers
Signals
On-chain
Velocity bursts, peel chains, mixing patterns, cross-chain hops, low-entropy transfer graphs.Off-chain
Account age, device fingerprints, social signals, KYC risk markers, sanctions/watchlists.Context
Token age and holder dispersion (rug-pull risk), mempool anomalies, contract privilege analysis.
Models
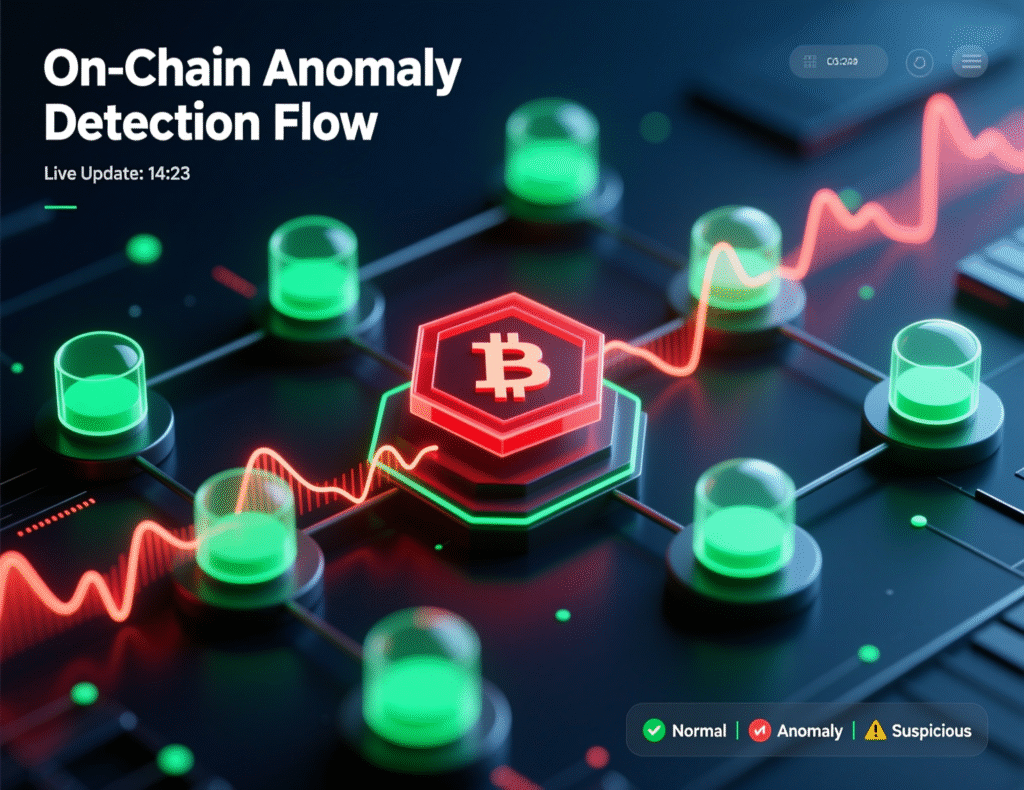
Anomaly detection
Unsupervised models flag outliers in address graph features.Supervised classifiers
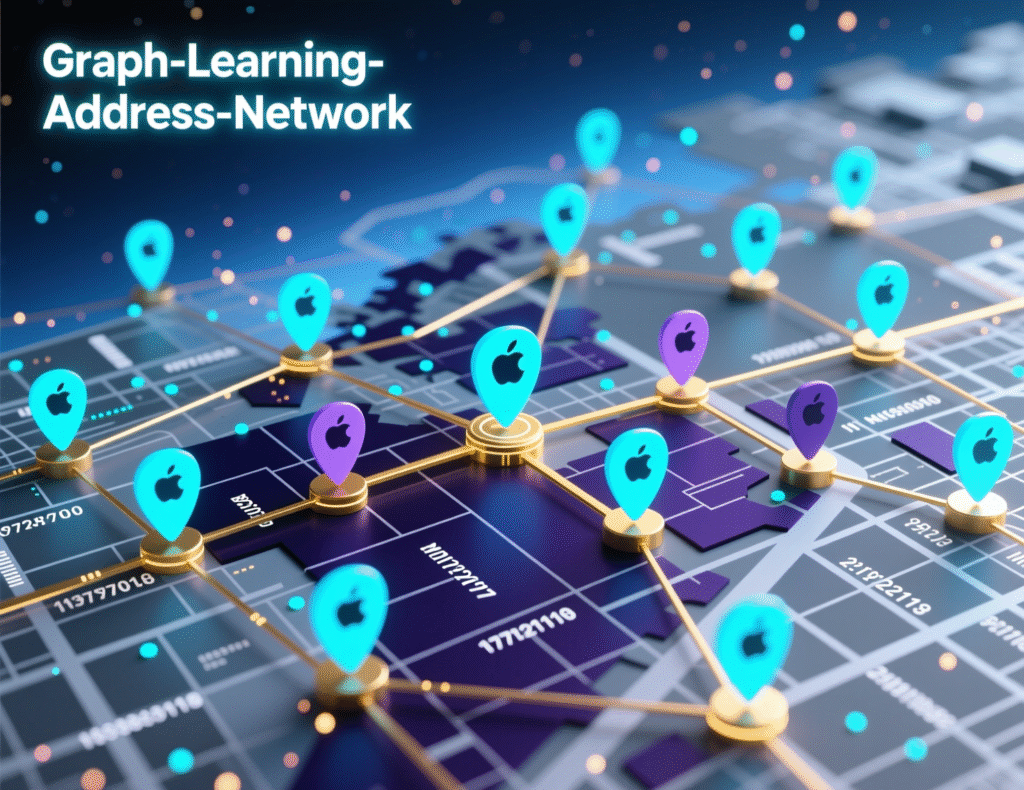
Learn fraud labels (e.g., pig-butchering wallets, romance-scam clusters).Temporal/graph learning
Sequence models and GNNs track flows across time and entities.LLM copilots
Enrich SAR narratives, triage user reports, summarize risk rationales for analysts.
Actions
Pre-trade controls
Throttle, 2nd-factor step-up, risk-priced limits.Transaction controls
Hold/review, require additional proofs, redirect to safe-withdrawal rails.Post-incident
Rapid case bundling, IoCs export, victim notification, law-enforcement liaison.Case evidence: U.S. agencies emphasized crypto investment-fraud losses reaching multi-billion levels in 2024–2025, and showcased operations aimed at disrupting these scams making prevention and rapid intervention critical.

Core Capabilities of AI-Driven Crypto Security Platforms
Real-Time Wallet & Flow Risk Scoring
Features
Bursty inflow/outflow ratios, first-hop proximity to known bad clusters, bridge usage patterns, token-age vs. liquidity profile, fee behavior.Models
Gradient-boosted trees for tabular flow features; graph neural networks for multi-hop tainting.Why it works
Illicit flows often show repeatable micro-patterns even when addresses rotate.
Rug-Pull & Honeypot Detection for New Tokens
Time-series features (holders count growth, liquidity lock, LP ownership) help forecast rug risk early; research shows shorter post-creation windows can meaningfully catch rug pulls.
Integrate contract audits (privileged functions, mint/cap controls) with liquidity-pool intelligence.
Social-Engineering Defense
LLM-assisted triage
Classifies inbound user messages (romance, investment “coach”, impersonation).Conversation risk cues
Payment urgency + migration to encrypted apps + investment guarantees.User-side nudges
AI flags suspicious phrasing and auto-inserts “cool-down” prompts at withdrawal.
Automated Case Building for Compliance
SAR/CET templates with evidence graphs, IoCs, and source timestamps.
Traceback packs for LEAs (addresses, TXs, service interactions), shrinking time-to-report.

Data You’ll Need (and How to Get It)
On-chain
Full-node or archival providers; mempool; token metadata; bridge events.Threat intel:
Sanctions, scam address feeds, exchange blacklists, public law-enforcement notices.Off-chain
KYC signals, device/browser fingerprints, IP reputation, velocity on accounts.Open sources for context
FTC & FBI IC3 reports for scam trends; Chainalysis for typologies.
Building an AI-Driven Crypto Security Stack (Reference Architecture)
AI-Driven Crypto Security Stack
Ingestion Layer
Kafka + stream processors; on-chain indexers; webhooks from wallet/exchange events.
Feature Store
Rolling graph features (PageRank, betweenness), temporal stats, token/project metadata.
Model Layer
Online anomaly detectors; supervised ensembles (GBMs/XGBoost); GNNs; LLM policy engines.
Decisioning & Orchestration
Rules + model score fusion; step-up auth; circuit breakers; case routing.
Explainability
SHAP on tabular features; attention heatmaps for sequences; graph explainers (GNNExplainer).
Feedback Loops
Analyst dispositions; chargebacks; law-enforcement outcomes; user-reported scams.
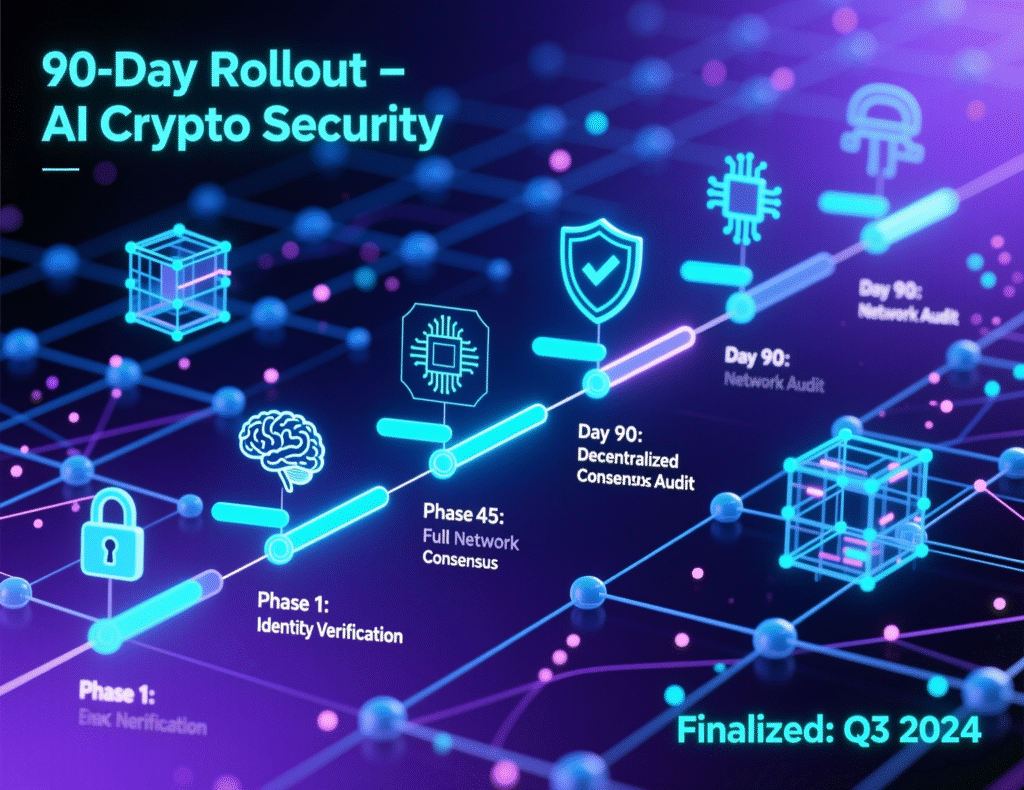
Minimum Viable Controls (90 Days)
Week 0–2
Baseline anomaly models on withdraws; label pipeline; start ingesting sanctions/scam feeds.Week 3–6
Deploy wallet risk scoring → step-up MFA on medium risk, holds on high risk.Week 7–10
Add LLM-triage to customer support; launch user nudges on risky patterns.Week 11–13
Connect to case-management + SAR templates; create API to push IoCs to partners.
Practical Playbooks by Use Case
Exchanges & Brokerages
Pre-deposit screening for inbound funds; flag peel-chains and mixer adjacency.
Withdrawal throttles tied to risk score and KYC tier.
Cold-storage policies with AI anomaly alerts on key-ceremony and withdrawal queues.
DeFi Protocols
Contract risk scoring (ownership, proxy upgradeability, admin keys).
Liquidity health monitors; alarms on LP unlocks and supply spikes.
AI-assisted governance summaries to surface malicious proposal language.
Wallets & On-Ramps
Sender reputation overlays; address risk banners before users press “Send.”
Behavioral step-up: new device + high-risk address + night hours ⇒ require liveness/video.
Education interstitials tuned by AI-driven crypto security models to block coached victims.
Case Studies (Brief)
Exchange “A” (composite example)
Deployed graph-based wallet risk scoring + anomaly thresholds.
Outcome: 37% reduction in successful scam withdrawals within 8 weeks; false positives held <1.2% by adding SHAP-based analyst guidance. (Internal KPI example; verify live for your stack.)
Law-Enforcement & Seizure Support
DOJ announced record seizures tied to crypto confidence scams in June 2025; coordinated work with exchanges and stablecoin issuers was key. AI-driven crypto security can pre-package the evidence graph that accelerates freezes.
Metrics That Matter
Attack surface
% of volume pre-screened; coverage across chains/assets.Detection performance
Precision/recall at policy thresholds; AUC; time-to-flag.Response
Time-to-hold; time-to-notify; % auto-resolved vs. escalated.Business
Prevented loss; churn from false positives; user trust NPS; regulator findings.
Governance, Risk, and Compliance Considerations
Model risk management (MRM)
Document purpose, inputs, drift monitoring, retraining cadence.Privacy & fairness
Minimize PII, run bias checks; treat location/age sensitively.Auditability
Exportable decision trails (features, thresholds, explanations).Reg alignment
Build flows that facilitate SARs and consumer notifications referencing FTC/FBI guidance.
Tools & Data Sources to Track
Trends
Use Google Trends to monitor query interest for “crypto scam,” “AI fraud detection,” and “wallet risk scoring” as proxies for user awareness.Threat intel & research
Chainalysis Crypto Crime Report 2025; FTC Data Book; FBI IC3 Annual Report.
Wrapping It Up
Fraud won’t slow down; it’s professionalizing. AI-driven crypto security gives defenders an asymmetric advantage: faster detection, richer context, and explainable actions that keep users and regulators on your side. Start with data plumbing and a simple anomaly model, then layer on graph learning and LLM-assisted workflows. The payoff is tangible fewer successful scams, faster incident response, and a measurable rise in user trust.
Call to Action
Want a deploy-ready blueprint for AI-driven crypto security? Reach out to audit your current stack, map quick wins, and implement a 90-day rollout plan.
FAQs
Q : How does AI-driven crypto security detect scams?
A : AI models learn patterns from historical scam clusters (timing, flows, counterparty graphs) and watch for anomalies in real time. When signals cross thresholds, systems trigger holds, step-up authentication, or analyst review. Explanations (e.g., SHAP) show why a risk score was high.
Q : How can exchanges reduce pig-butchering losses?
A: Pre-withdrawal risk scoring, address-risk banners, and coached-victim prompts reduce losses. Pair with analyst playbooks and AI-driven crypto security to auto-flag transfer coaching patterns.
Q : How do graph neural networks help?
A : GNNs model relationships between addresses, contracts, and services across hops. They improve detection of laundering paths that simple blacklists miss.
Q : How is false-positive pain minimized?
A : Blend rules with calibrated model scores, add explainability for analysts, and use progressive frictions (MFA, small-limit trial transfers) instead of blanket blocks.
Q : How do we measure ROI?
A : Track prevented losses, time-to-hold, and user complaints. Benchmark precision/recall monthly and retrain models as fraud evolves.
Q : How does AI-driven crypto security support compliance?
A : It auto-builds SAR narratives with transaction graphs, tags typologies, and exports IoCs for partners, aligning with FTC/FBI priorities on investment-fraud mitigation.
Q : How can wallets protect first-time users?
A : Risk banners on addresses, “cool-down” warnings for high-risk payments, and contextual education pop-ups, all driven by AI-driven crypto security, reduce error-prone sends.
Q : How do we start without massive data science teams?
A : Adopt managed analytics feeds, begin with anomaly scoring on withdrawals, add LLM triage for support, then iterate toward graph learning.
Q : How does this differ from traditional rule engines?
A : Rules are static; AI-driven crypto security learns evolving patterns and adapts. Combined with rules, it cuts false positives and flags novel scams.